Today I’m glad to continue our journey for Setup an Enterprise Subordinate Certificate Authority deployment “Installing – Configuring Subordinate CA as Online Issuing CA”
Certificate Authority Purpose
For part 1 please check the link bellow
let me start explaining a little bit about Enterprise CA
For my needs I will install my own CA, so I can use it to issue any number of certificates to support for the following Servers and Services with free charge.
- VPN
- RD Gateway
- Lync (Skype for Business) Servers Internal Access
- Lync (Skype for Business) Servers External Access
- Web Server
- Web Services
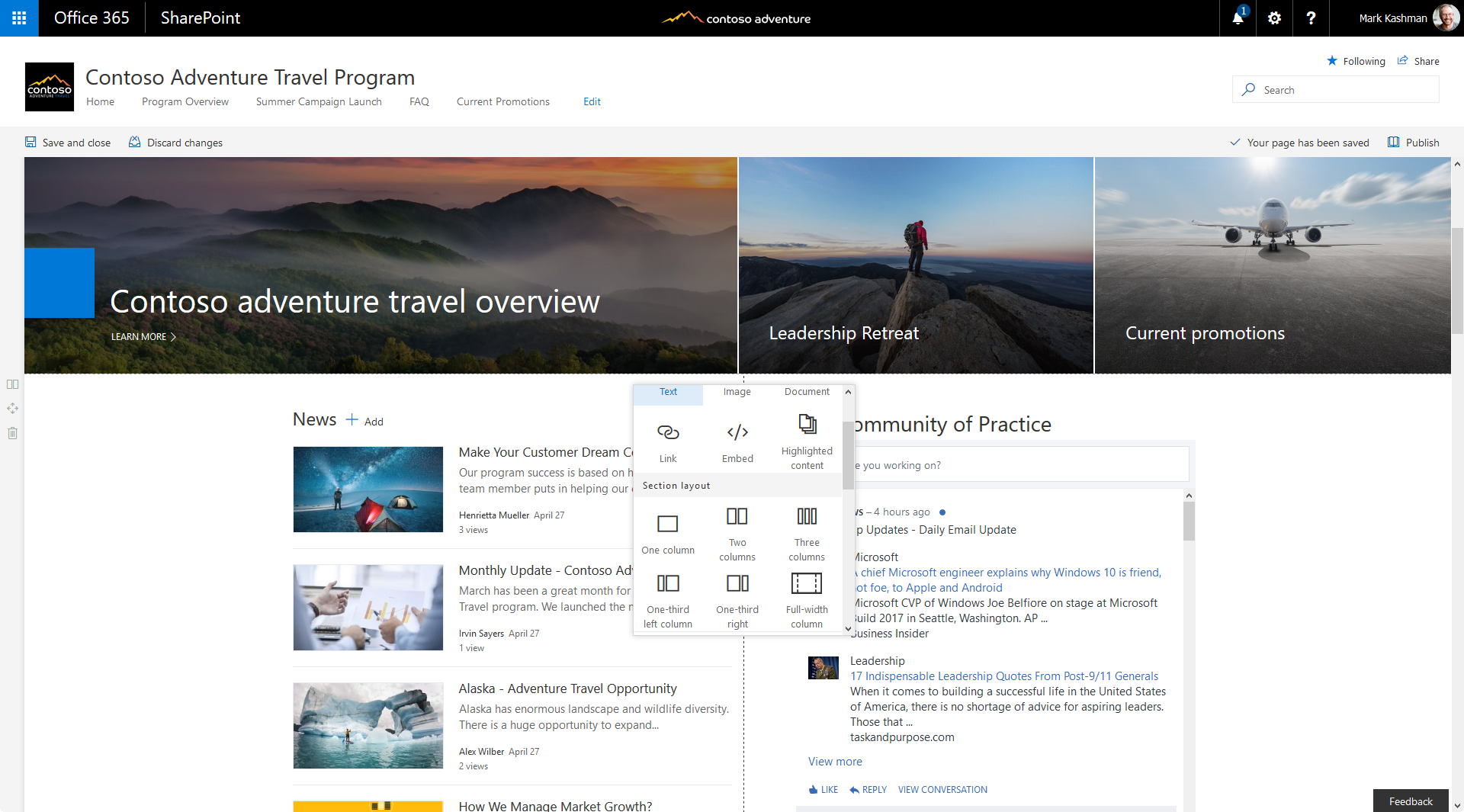
- SharePoint https access
- Office WebApp
- DirectAccess
- Others …
This CA removes the cost required to buy a dozen of certificates to support those services
Before I start let’s know what is Certification Authority (CA) and what is the CA main purposes?
Certificate Authority (CA) is well-designed and highly trusted service in an enterprise that is trusted to sign digital certificates. CA verifies identity and legitimacy of company or individual that requested a certificate and if the verification is successful, CA issues signed certificate.
The main purposes of the CA are
- Issue certificates
- Revoke certificates
- Publish AIA and CRL information
By doing this, the CA ensures that users, services, and computers are issued certificates that always valid and validated. Before start let`s discuss this diagram 🙂
Enterprise PKI Design
Being diligent, I sketch out what we are about to do first.
My Servers Information
| Server Name | OS | Role | Workgroup/Domain |
| RootCA | Windows Server 2012 | Standalone Offline Root CA | Workgroup |
| IssuingCA1001 | Windows Server 2012 | Enterprise Subordinate CA | Domain Joined |
| DC01 | Windows Server 2012 | Domain Controller | NAN |

- DC01 – an active directory domain controller called msallal.com which connected to several machines and will be the central point for distributing the certificates over domain joined machine
- ROOTCA – Standalone offline Root CA which will generate the private key and trust the Issuing CA to generate a certificate after that it will be kept offline for the next 5 years to renew the trust with IssuingCA1001. A Root CA is special in that it`s certificate is self-issued. This mean that the certificate’s issuer name and subject field contain the same distinguished name
- IssuingCA1001 – is an Enterprise Subordinate CA which will issue and revoke the certificates as needed.
Phase 1: Enterprise PKI Deployment – Subordinate CA
For this scenario I will complete the implementation of 2 tier PKI hierarchy which contains offline standard Root CA server and online enterprise subordinate CA.
Prepare your servers with latest update and enforce your organization policy and make sure to join IssuingCA1001 to the DC. let`s go…
Installation
- on the IssuingCA1001 server, click Add roles and features… Next – Next – Next – select Active Directory Certificate Services

- Next
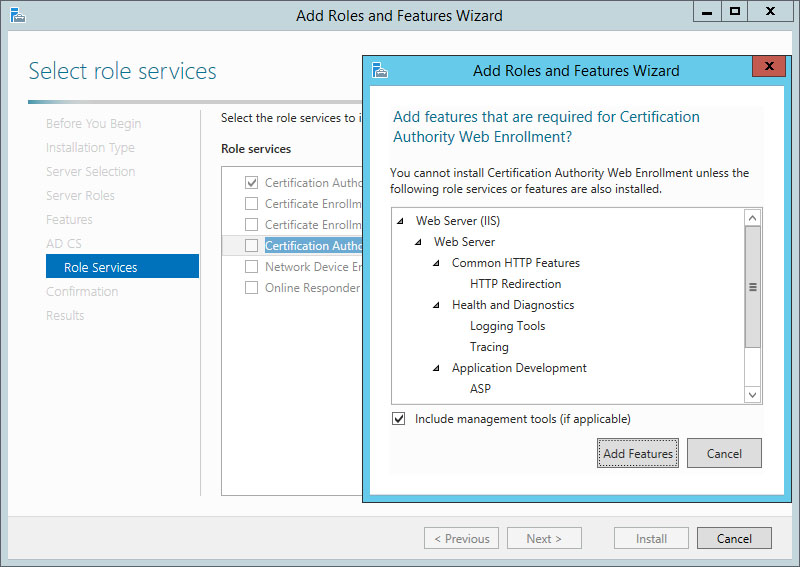
- Make sure Certification Authority and Certification Authority Web Enrollment are selected

- Install
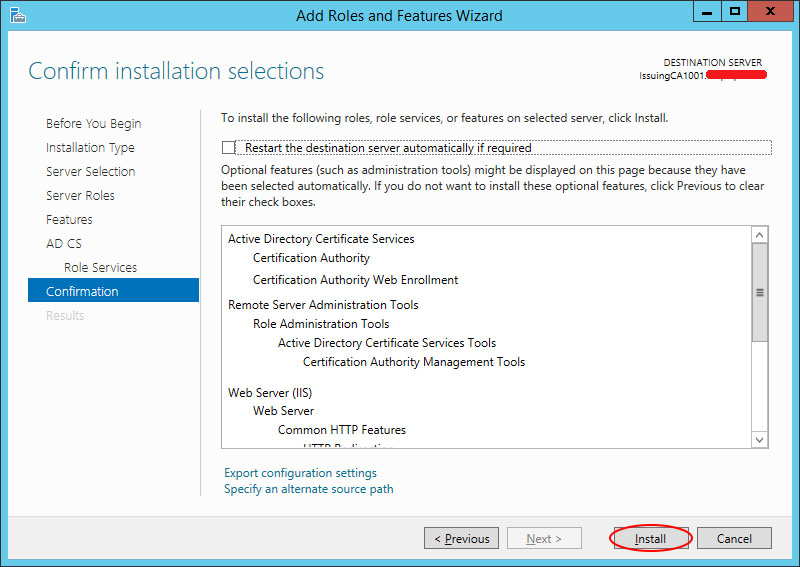
Configuration
You can start configuring the AD CS form here or from the server manager notification


- IssuingCA1001 should be a domain joined, user with domain Admin privilege required
- Next
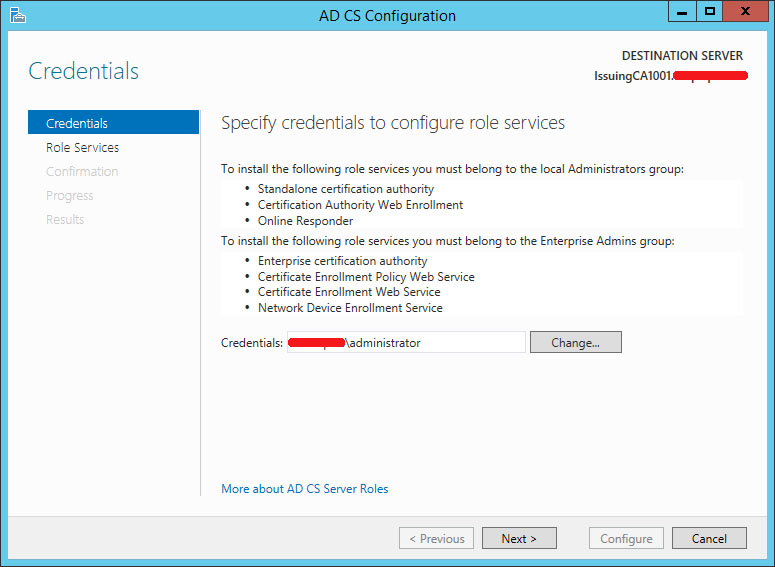

- Choose Enterprise CA
- Next

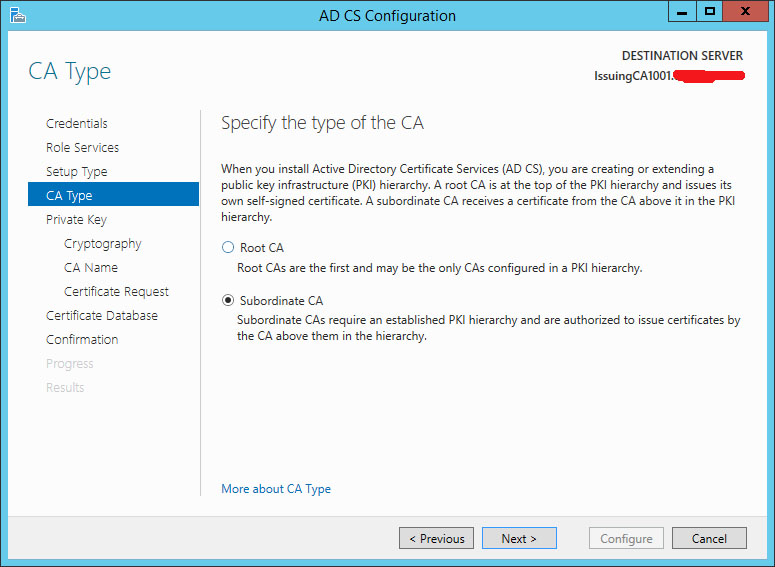
- Choose Subordinate CA
- Next
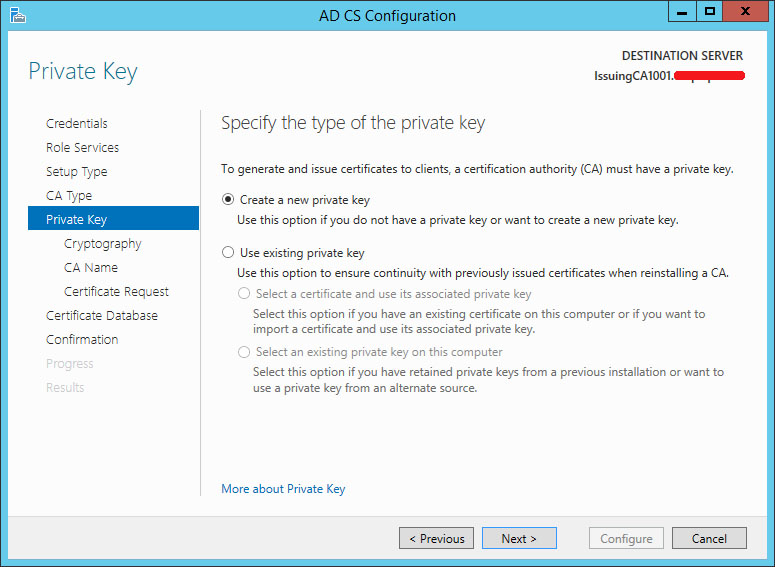
- create a new private key
- Next


- Save the certificate request file, which will be imported to the Root CA to trust the subordinate, we will use it in phase 2
- Next

- Configure

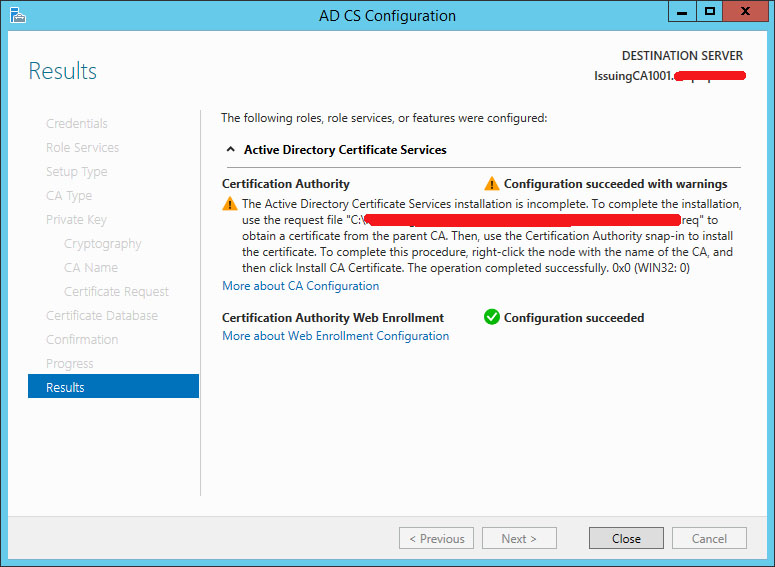
Phase 2: Trust Subordinate CA by Root CA
To make the subordinate server responsible for issuing a certificates for your organization you should make trust between Root CA and Subordinate CA, by submitting the request file that created in subordinate configuration above to Root CA and get back the resulted certificate to the subordinate.
Go to the offline ROOTCA server – open Certificate Authority – All Tasks- Submit new request
choose the .req file created while configuring subordinate CA phase 1 – open
the certification trust now is done, but in pending state, we should issue that certificate
All tasks – Issue
Now its in issued certificates list
Double click at the certificate, it should look like this
go to certification path to view the certificate server hierarchy, it should have two level hierarchy Root CA at the Top – Sub CA (Issuing CA) under RootCA
now we need to export the trusted certificate back into the subordinate server – choose Copy to File
Choose .P7B and tick Include all certificates in the certification path if possible
save the file – and copy it to the IssuingCA1001 server (Subordinate server) and move on
in IssuingCA1001 server open Certification Authority – All Tasks Install CA Certificate, choose the exported certificate that come from Root CA
Certificate service now is in running state, You should see the small green icon for the sub-CA certificate authority now.
If not, go back to check the CRL and AIA settings, again, all of the location defined in CRL and AIA must be accessible in server IssuingCA1001 server, which means you should have a copy of the CRL files in C:\Windows\System32\CertSrv\CertEnroll and the IIS site as well.
Checking the CRL and AIA status
- Run pkiview.msc
Conclusion
Awesome, done for now.
At this moment, we have deployed and configured an enterprise subordinate CA…
Next, check the part 3 to publish the root CA certificate to your infrastructure using Group Policy
Thanks
[inhype_block type=”showcase4″ block_title=”More from Mohamad Sallal” block_subtitle=”Recommended” block_posts_type=”random” block_categories=”” block_posts_limit=”4″ block_posts_loadmore=”no” block_posts_offset=”0″]